So if you I build a second AP like this:
it's going to use the same DHCP server as the internal WIFI. Obviously, because it's on the same bridge (switch) interface. I always wondered how they are still separeted by the RouterOS? The answer is Mikrotik's genius Layer2 firewall called Bridge filtering.
But you discover an embarassing problem if you have more IP subnets (e.g. VPN networks over pub net) and also want to accept the guest wifi filtering to them. One simply can't utilize Layer2 filtering over Layer3 routing and, of course, there is no work vice versa.
Soution: forget the built-in bridge and create a new bridge only for your guest wifi.
/interface bridge add name=bridge-guestwifiAdd a new security profile for guest if you happen to still doesn't have any:
/interface wireless security-profiles add authentication-types=wpa2-psk mode=dynamic-keys name=guestwifi wpa2-pre-shared-key=topsecretpasswordAdd your new slave interface:
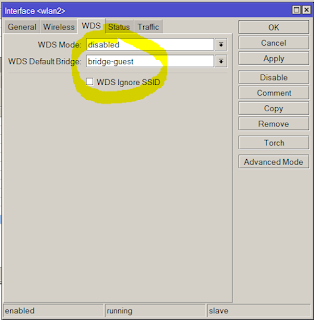
/interface wireless add disabled=no mac-address=D6:CA:6E:4F:54:28 master-interface=wlan1 name=wlan2 security-profile=guest ssid="For Guests" wds-default-bridge=bridge-guestwifiand link these 2 to each other.
/interface bridge port add bridge=bridge-guestwifi interface=wlan2
So far so good. Layer2 filtering is done now. But now the guests are totally separeted from your DHCP server so you need to create a new, dedicated DHCP pool for them. It requires a new address and subnet.
/ip address add address=192.168.100.1/24 interface=bridge-guest network=192.168.100.0 /ip pool add name=guest ranges=192.168.100.100-192.168.100.254 /ip dhcp-server add address-pool=guest disabled=no interface=bridge-guest name=guest /ip dhcp-server network add address=192.168.100.0/24 dns-server=192.168.100.1 gateway=192.168.100.1
Lets suppose that you have such a source nating rule that nats anything that is going out to the internet:
In that case we have good news. You don't have to set up any more nat rule because the guest network will hit the above rule. But it's not secured yet. The following Layer3 high priority firewall rule will take care of them:
/ip firewall filter add action=drop chain=forward in-interface=bridge-guestwifi out-interface=!ether1-gatewaySo from now on, guests are denied to go anywhere but the public internet.




Nincsenek megjegyzések:
Megjegyzés küldése